[Updated 19th March 2020]
Channel 4 reality tv programme Hunted manages to get you to suspend disbelief (you quickly ignore the obvious presence of a camera person with each fugitive) as around a dozen "fugitives" are hunted by a team of hunters with
the simulated (in the case of CCTV and ANPR) powers of our UK surveillance state.
It is worthwhile thinking about some of the techniques used in the 4 series so far and how proportionate their use is in any real
cases, apart from the very most serious criminal or national security scenarios.
Twitter hash tag: #Hunted
Channel 4 Hunted home page
Hunters' techniques already used
DVLA vehicle Registered Keeper check
ANPR - Automatic Number Plate Recognition
GPS / Mobile phone vehicle tracking device attached to family / friend's car
Private aeroplane flight plans
AIS - Automatic Identification System boat / ship beacon mapping
Public CCTV - realistically not available in real time except at transport hubs
Bank ATM CCTV
Bank ATM card transaction alert
Mobile hunter teams in distinctive Volvos or BMWs etc. (N.B. product sponsorship deals)
Mobile hunter teams in less distinctive white van etc.
Helicopter surveillance - limited airtime
Drones - limited battery, not so great in bad weather.
N.B. neither helicopters nor drones are likely to be used in near major airport flightpaths
Directed Surveillance "stake out" of fugitives family / friends homes using remote cameras and human watchers.
Sniffer dogs
Mobile Phone subscriber details - registered or burner ?
Mobile phone new SIM card in known IMEI handset
Mobile Phone friendship tree - other numbers called / recived when, how long for
Mobile Phone Location Data - targeted
Mobile Phone Cell Tower dump analysis to detect candidates for people who picked up a fugitive in a relatively isolated town or village at a certain time and then phoned their mate to arrange a further lift or accomodation. Harder to do in a City, but there are more Cell Towers per square kilometre so Location fixes are more accurate and useful to the Hunters ground teams if nearby. N.B. usualy a maximum of 256 simulataneous calls per Cell which can be up to 35 Km wide in the Countryside
Cities can have several micro Cells per street or busy shopping or transport area so give more accurate Location fixes, but make it easier to lose track of a burner phone if it is switched off quickly after use and the fugitives move out of the small Cell area fast enough.
snail mail intercept of letters / postcards
Social Media monitoring
Twitter
FaceBoook
Contact chain mapping / visualisation - IBM i2 Analysts Notebook etc.
Hacking of seized laptops, iPads, SmartPhones after a visit by hunters
Covert Hacking via USB malware of laptops , iPads, SmartPhones during a visit by hunters
Forensic analysis of paper writing pads and note books etc. to reveal writing impressions on the blank paper
Geotagging of SmartPhone Location history from seized phones, showing previous travel locations / possible local friends networks
Encouraging children and other casual occupants of a fugitive's family or friends or casual helper's home to talk about the exciting / famous visitor(s) and where they are going
Local radio and newspaper and social media Reward Appeals
£££ cash rewards for tips to publicised phone line or email address
Bribing £££ with reward offer other casual occupants of a fugitive's family or friends or casual helper's home to talk about the exciting / famous visitor(s) and where they are going
Psychological pressure especially on fugitives with young families - get them to meet family / friends who are being watched.
Social Media taunting of fugitives supected of being very competitive / with strong egos, to get them to post a revenge taunt video or photo, giving hunters clues as to their recent location.
"ghost agent" - Non-hunter private investigator / CHIS acting as undercover agent e.g. picking up hitchikers and taking them to the hunters
Social Engineering / blatantly lying to casual contacts on the phone or in person contradicting the fugitives story to get information on them e.g. drop off point
Social Engineering / offering a financial reward to casual contacts on the phone or in person to get information on the fugitives e.g. drop off point
Hacking in to an Android mobile phone's Google Voice Search search history voice recordings
Hacking in to a Google account showing Google Maps search history
Find from bank records that recent graduate students have money problems.
Exploit this by freezing their bank accounts.
When they are recovering from wet wild camping at a local inn, the Bank Card Transaction Declined pinpoints their exact time and location to the Hunters.
Using up almost all of their cash to pay the bill, forces them to reach out to their (monitored) network of friends
Planting remote CCTV cameras inside and outside a fugitive's sister's cottage - picks up a friend who has gone there to arrange a rendezvous
Physical access to a fugitive contacts' mobile phone - scrolling through recent contacts,
taking screenshots and sending them to HQ for analysis.
Physical access to a fugitive contacts' mobile phone - accessing Deleted Messages remotely
Get real time Mobile Phone pings / Location of a phone travelling down the M1 motorway
e.g. Cell Tower every 10 minutes network handshake (even when the phone is not actually in use)
Offering money reward to captured fugitives to either betray their partners still on the run or to give details of the nominated extraction point.
(previous series offered only a few hundred pouns, February 2019 finale tried £4000 without successs)
Financial bribe offer to captured fugitive made more likely by faking the capture of his partner , using loud cheering and voice samples from social media video clips.
Bellingcat style geolocation analysis of buildings visible through windows etc. of videos or photos posted on social media to narrow down the exact location from distinctive landmarks (no angle of the sun / shadows etc. analysis for Latitude shown yet, but this is possible)
Bugging the taxi which takes a captured fugitive home, so that they give clues from chat with the driver, about the captured fugitive's still on the run partner's plans e.g. that they know someone with an aeroplane
Access to military service records showing that retired 79 year old fugitive Mervyn had been in Territorial SAS and Military Intelligence.
BMW Assist vehicle telematics regualar location fixes and data on when and where the engine is stopped or started, hinting at rendevous points.
Editing together a number of Voice Notes on a captured phone to fake a message to sew distrust with the captured running partner of a fugitive.
Implication tht he will not share the £100,000 prize money with her, she is offered a chance to name a price for information
She tell the hunters that she is not a snitch
Sending a fake burner phone text message to a fugitive's friend from work (identified through social media network link analysis), asking for help to be extraced from the caravan location she has hidden them in.
She does try to authenticate the text message by asking what her dogs' names are. However the hunters find this quickly from FaceBook.
(should have had a pre-arranged duress code / pre shared secret when they were all face to face.
The hunters follow her vehicle without being noticed (classic road surveillance techniques)
Hunters techniques - not yet seen
internal Bus and Train CCTV - can't be real time
London Oyster Travel Card data - some early posters, but was it actually used ?
London Oyster travel Card combined with TfL CCTV
Mobile device Wifi Probes trying to automatically connect back to out of range home or office Wifi
Mobile device Wifi Probes trying to automatically connect back to out of range but distinctive list of "free" WiFi Access Points
GPS coordinates embedded in a digital image posted on social media - Exif metadata - like John McAfee EXIF Data May Have Revealed Location of Fugitive Software Tycoon John McAfee
Digital camera flaw analysis of digital image posted on social media to identify other photos taken with this (borrowed ?) device, which may lead to the owner
GPS Fitness tracker social media app (e.g. Strava) infiltration and analysis to identify competitive runners or swimmers or cyclists who may be contacts
Equivalent of Cell Dump using e.g. Google Maps - who has been downloading map tiles of a certain area at the relevant time for navigation ? Do their
other Map downloads give a clue as to where they are heading ?
GPS navigation device route data from "seized" vehicle that gave the fugitive a lift
GPS navigation device route data from "seized" SmartPhone of a driver gave the fugitive a lift
GPS / Mobile Phone Network tracking of vehicles fitted with E111 emergency "call the ambulance if in a crash" technology
Private Investigator / CHIS cruising the initial Start location, or, when identified the Extraction point as a mini cab driver / Uber driver to pick up fugitives and lead them into the arms of the hunters.
Google Auto Android in car navigation systems using Google Assistant voice recognition and Google Maps on a BlueTooth linked Android mobile phone- .mp3 file forensic artefecats may betray location of a rendezvous or drop off
https://thebinaryhick.blog/2019/01/30/ka-chow-driving-android-auto/
Probably the same for Apple CarPlay and a BlueTooth linked iPhone
Hunters sending a "burner" phone to family / friends of fugitive, pretending it has come from the fugitive, to encourage them to contact them on the fugitive's secret burner phone
N.B. Intercept of such a burner phone and bugging / monitoring thereafter by the hunters
Fugitives' techniques already used
Wigs, and change of clothing disguises
Hats and scarves - most CCTV looks downwards, so these can make it harder for hunters to pick out enough identifying detail of your face
Human decoy disguised as the fugitive
Initial start point disguising of luggage e.g. rucksacks hidden in airline style luggage cases on with wheels
Heading for the countryside along canals etc without urban CCTV
Heading for the countryside to a network of friends
Heading for cities with network of friends
Having a huge network of friends or fans e.g. tv / pop stars with fans, political activists or Free Masons
Burner phone - not enough to swap SIMs - phoning a "watched" number hardly slows the hunters down at all
Disinformation - planting false clues for the hunters
Social Engineering / Blagging lifts / hitchiking
Not giving up when blagging a lift, just jkeep trying until someone is going the way you want.
Social Engineering / Blagging the temporary use of a stranger's mobile phone to make a call
Social Engineering / Blagging the temporary use of a stranger's computer to use the internet etc.
Using an online mobile phone app simulator to send an App message to a physical SmartPhone
Bicycles - no ANPR
Motorbikes / scooters - less chance of ANPR
Taxis - quickly jumping in to e.g. London black cab taxi is better than waiting in the open for a bus, but risks hunters getting drop off details from the driver / company or even internal CCTV
Speed Boat
Helicopter
Celebrity fugitives can hide in a locations which are heavily fortified (Parliament) or surrounded by private security cameras and guards
(multiple private holiday homes estate owned by rich people) inaccessible to the Hunters.
Well resourced (Celebrity) fugitives seem to have multiple helpers and decoy vehicles - stretch the Hunters' resources
on a getaway.
Letting down the Hunters' Volvo car tyres worked at least once !
Hiding somewhat from village CCTV by using a closely held umbrella hiding your face
- quite normals in wet and windy Wales.
Not being seen to be travelling together on a train - but only if you do not need the comfort and support of a travelling partner when under stress
Asking someone to pass a note to your friend in the next train carriage - good but limited uses.
Getting off a an infrequent rural bus service *before* it reaches its destination in the nearest town (Abergavenny)
and heading into the countryside.
Taking aa bus from Wells to Bristol but getting a lift to partway along the route rather than starting from the CCTV monitored bus station.
Wearing a white hat amongst a crowd of Panama hat wearing tourists and locals.
Pre-arranged Word Code e.g. "Pepsi Max" delivery time / location in SMS texts - if too anamolous from the "normal" usage
then these stand out suspiciously and Cell Location gives the ganme away.
(Should really use an Encrypted Messenger e.g. Signal Messenger or WhatsApp)
Use of pre-assumed obscure knowledge as a word code e.g. "meet me at the place that I first worked at in London" - N.B. Celebrities especially vulnerable to such a reference being quickly decoded via a Google searchulnerable
Not running immediately (so as not to draw attention) when you have spotted / heard a reconnaisance Drone overhead, then getting under wooded cover and waiting for the limited battery life to expire like the Royal Marine Matt Mason did.
Fugitive's wife using FaceBook App to call a friend in contact with the fugitives (Communications MetaData still available to the Hunters)
Splitting up temporarily so that fugitive A can meet his sister. Other fugutive B posts a real time Instagram video with a friend disguised as fugitive A, to draw away the attention of then hunters.
This works, but later CCTV analysis shows the deception (too late).
Hand held walkie talkies to keep in touch with each other whilst approaching a possible meet up.
Old school no social media presence at all.
Managing to withdraw £100 cash from a bank branch cashier in a strange town, without your bank card.
Future fugitives should practice this and memorise account number, recent transactions and offline / phone banking security questions.
Using Xbox Live VOIP Voice Over IP calls between gamers - the hunters cannot (yet) intercept this, but Xbox users are usually obvious amongst fugitives' social media
A stranger helping a fugitive uses a Virtual Private Network VPN to connect to the internet "without being traced" to view the social media campaign Wanted Poster
Pretending to have split up from a fugitive's partner, phoning youe mother, knowing the hunters will trace the location of decoy phone call, but quickly escaping from the location by vehicle.
Fugitives' techniques - not yet seen
burner phone to burner phone communications to friends or family
WiFi or Ethernet connection hacking to get "anonymous" access to the internet
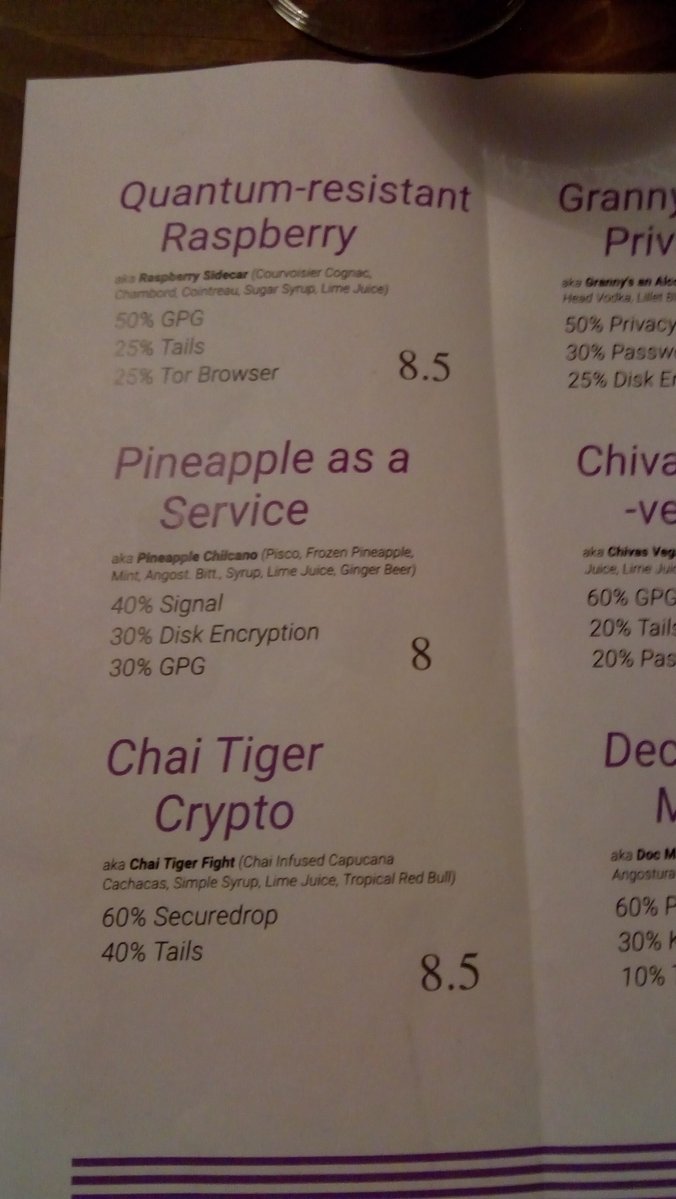
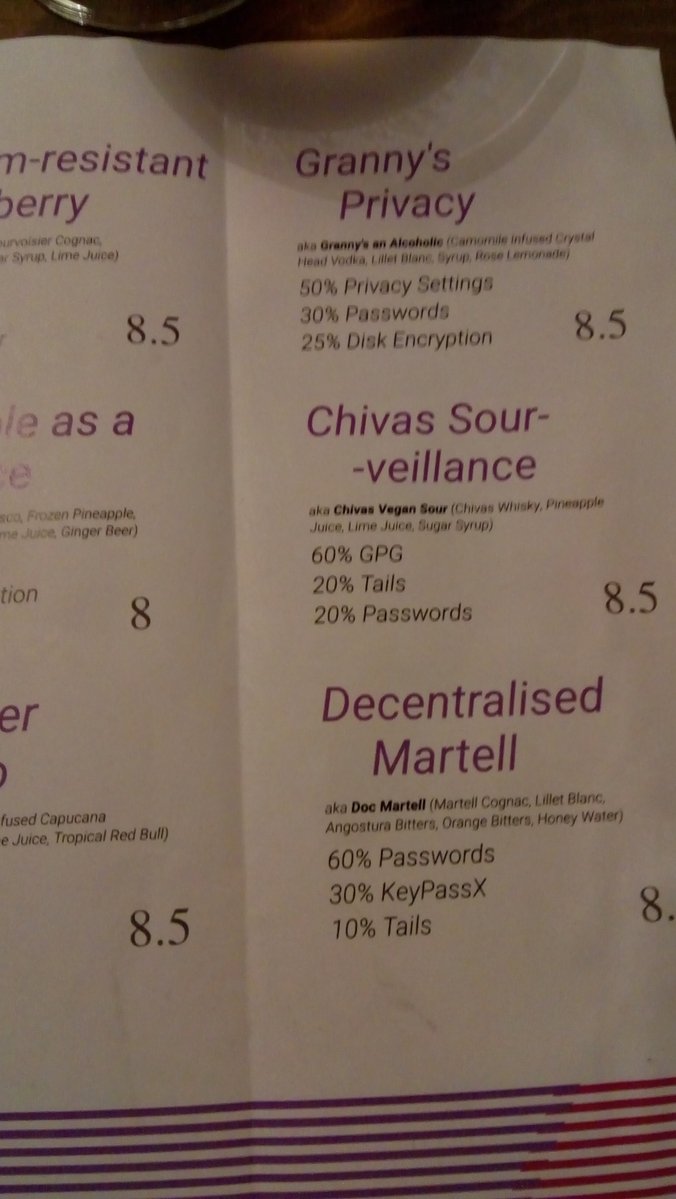
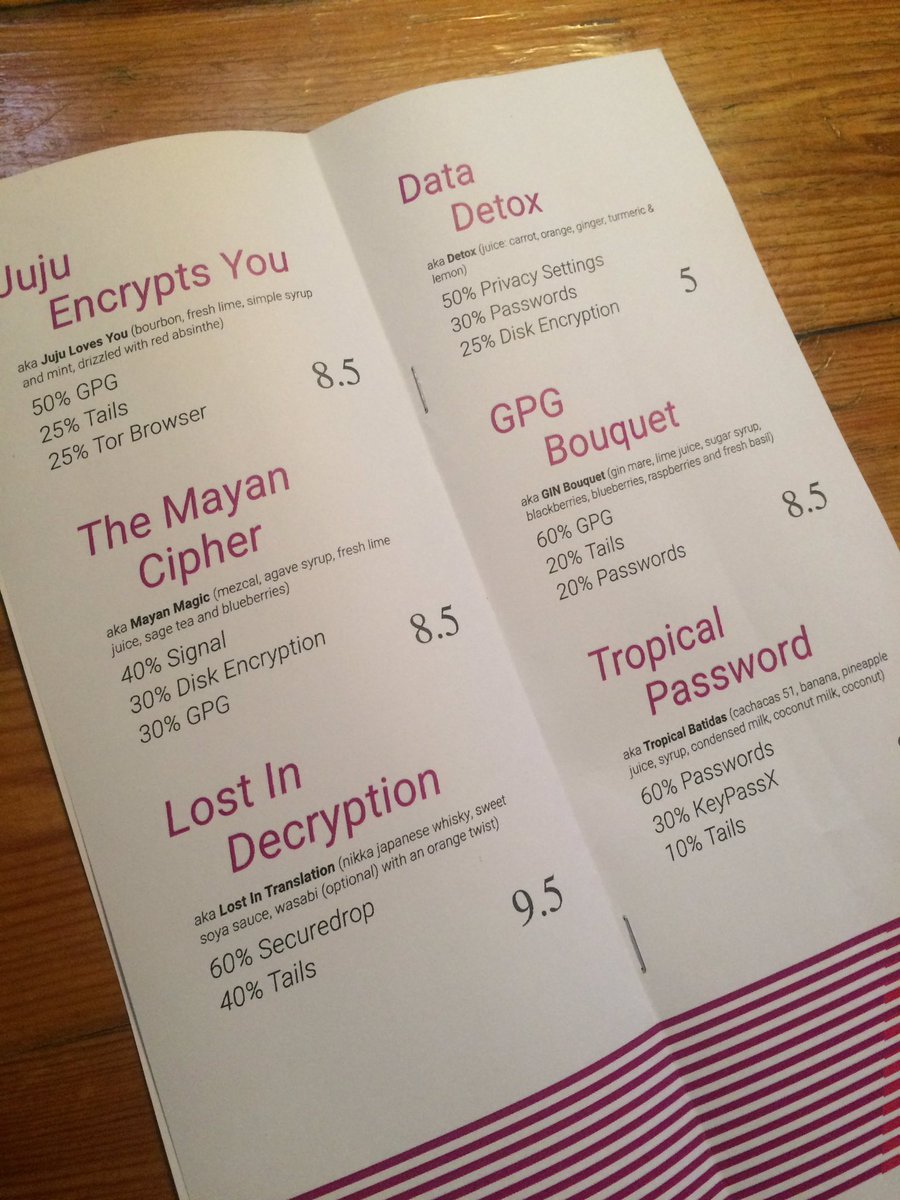
Use of Tor or a foreign based VPN
- Tor project https://www.torproject.org/
- Orbot for Android https://play.google.com/store/apps/details?id=org.torproject.android&hl=en_GB
- Onion Browser for iOS https://itunes.apple.com/gb/app/onion-browser/id519296448?mt=8
- FaceBook via Tor .onion address https://en.wikipedia.org/wiki/Facebookcorewwwi.onion
Use of mobile phone 3G or 4G PAYG data packages to get mobile internet access on the run
Use of Satellite Phones - easy to intercept but hard to jam or find the exact location of
Counter bribes - if social media / local press & radio campaign offering £200 , offer people giving you lift £500 as you have a chance of winning £100,000
Getting friends to run a counter Have You Spotted this Hunter social media campaign with £££ rewards on offer - fake Wanted Posters unnerved them a bit previously
Infilitrating / surveilling the Hunters' HQ
Covertly grabbing identifiable WiFi and BlueTooth MAC addresses and Probe SSIDs etc. from the Hunters, when a family member or friend is interviewed
Getting a ticket / bus / train bound e.g. for London but getting off at a stop before.
Getting a ticket but not catching the bus / train / tube / aeroplane etc. at the nominal start, but at a later intermediate stop along the journey.
Purchasing multiple transport tickets or a "roam anywhere" ticket
Using an Amazon or other courier to get a package with a burner phone to a friend or family member via an Amazon Locker or other non-home parcel pick up point
Pair of fugitives splitting up so that one of them can distract the hunters near the extraction point, letting the other escape / win the prize
Other contestants spotting you near the extraction point and dobbing you in, to distract hunter resources so they vcan escape / win the prize
USA Hunted technique of enrolling the good looking fugitive(s) on dating apps in an area, and then posting £££ reward info to the people who have seen or even flirted with the fugitives
Radio Monitoring the airwaves / listening to walkie talkie radio of approaching hunter teams
Radio Detecting the presence of hunter teams via their bluetooth headphone / microphones
Uber app taxi alternative - given the snooping and mapping, is this worth the risk of central digital betrays to the hunters or malware a cloned SmartPhone ?
Setting up pre-arranged series of random code words (memorised not written or stored electronically) with family / friends either as a word code about specific locations, dates, times or as authenticators of ad hoc messages(hunters have intercepted and faked postal mail messages)
e.g. getting a friendly stranger to email or social media a message to family / friends including a code word to prove its authenticity
Mobile Phone Encrypted Messenger Apps over public WiFi or via burner Data SIM
- Signal Messenger https://signal.org/
- WhatsApp https://www.whatsapp.com/
- Wire https://wire.com/en/
- Threema https://threema.ch/en
- Telegram Messenger https://telegram.org/
Pre-arranged DeadDrops for money or burner phones or messages to / from family & friends etc.
Using a prepaid Virtual Post Box service to scan and electronically forward postal mail in another country, to allow fugitives to remain in contact
with their family, friends network
https://britishexpatguide.co.uk/the-best-uk-virtual-postbox-for-mail-forwarding/
Fugitives' Errors
Buses and Trains are a bit of a trap unless hunters think you are not using them
Contacting loved ones - an essential part of the dramatic tension of the show
Taunting the Hunters
Not taking *all* available cash at an ATM
Ignoring multiple sightings of distinctive hunters' Volvo cars
Being noticably loud / obnoxious to pub / hotel staff
Failing to tip pub / hotel staff - no reason for them not to claima £££ reward if offered
Expecting a taxi driver not to give up info on drop off point if offered £££ reward
Wearing a bin liner over your head makes you stand out on CCTV, *not* the reverse !
Just changing the SIM in your mobile phone handset does nothing to stop it being tracked via the IMEI serial number sent with every voice or data call.
Getting too paranoid about real time CCTV in rural areas - the Hunters might be able to get yesterday's footage, but it could take a week
Not being paranoid enough about real time CCTV in major city centres and bus / rail / airports etc.
More dominant / arrogant partner destroying the trust of the other fugitive partner when under pressure, by doing something percieved to be selfish, without consulatation, leadng to a break up.
Not keeping a sharp lookout for Volvo cars
Trying to get accomplices to trap a Hunters's car at a rendezvous you have tipped them off to by taunting them
(a couple of fugitives have tried this - very risky)
Trying to crawl past CCTV cameras like caterpillars
Putting a cover over a CCTV camera but being recognisably filmed actually doing it.
Only using 1 burner phone - the family / friend / contact *also* needs a burner phone they never use
Forces the hunters to try Co-Traveller / Cell Site Dumps which need lots more analysis which might not be feasible in time to be useful for the next meeting / pickup / drop off
Family member's mobile phone ping location reveals approximately where they have met a fugitive - regardless of wjether the phone was used during the journey to and from the rendezvous.
Turn the phone off at least for e.g. an hour's travel time before and after the meeting.
Drawing the curtains on the ground floor during the day time, making the address stand out to the hunters scanning the street.
Hunters' Errors and Limitations
Most of the power and resources are with the Hunters, so most of their near misses or failed captures have been literally only by a few minutes or seconds (with approriate suspension of disbelief)
They have fallen for a few of the wily / arrogant fugitives false trails and decoys i.e. deliberately false clues as to location
They have misjudged people who have helped the fugitives e.g. offering a £££ reward / bribe, and then thinking it was working only to be told that the "informant" had changed their mind or would not "grass" for the small sum offered.
The randomness of some of the fugitives hitchhiking has caused the Hunters problems in trying to guess where they might be
Where the Hunters were seen to be blatantly lying to get information, they risked the ire of the tv audience.
Despite the power of thermal imaging from (limited endurance) helicopters or drones, so far, each of the times this technology has been used by thehynters, it has only found false positve wild animals or innocent members of the public, rather than the fugitives, who it has, of course frightened and added to their stress levels, but not enough to matter.
ANPR on very busy roads e.g. M1 motorway is available, but not in real time if the exact
vehicle being searched for is not (yet) known simply due to the volume of traffic.
Using identifiable black Volvo vehicles which tip off the fugitives tht the ground hunters are close by.
Beware of the Extraction Point Instructions communication method
Web bugging the USB with the fugitive extractiomn instructions to betray the IP address and thus approximate location of where it was opened
(fugitives should make sure the internet is disconnected if they need to do this again)
Accessing a pre-recorded phone message: ""By accessing this message your exact location has been revealed to the hunters!"
Fugitives should use a burner phone or one borrowed from a stranger or get a friend to do this (if they have secure communications with them)



































Recent Comments