It looks as if WikiLeakS.org / Julian Assange's stupid decision to abandon use of PGP encryption, back in 2007 has come home to roost, with the revelation that they idiotically re-used a symmetric encryption key password and ineptly published a full archive of the controversial US Embassy / State Department Diplomatic Cables on BitTorrent peer to peer file sharing networks
The fact that they published this unredacted archive at all via BitTorrent shows how chaotic and incompetent Julian Assange and his motley crew of inexperienced acolytes had become after Daniel Domscheit-Berg and the "Architect" left them.
The end result is that there are now many people around the world, including all the repressive governments mentioned in the quarter of a million Diplomatic cables who can now simply search for key words like (strictly protect), to find the names of informants and information sources who have been in contact with US Embassy diplomats and who could therefore now be easily persecuted.
See the Cryptome.org for a direct file link to z.gpg or to this torrent link to the same encrypted compressed file via BitTorrent peer to peer filesharing.
John Young's evident glee that WikiLeakS.org have now published the full, unredacted archive of US Diplomatic Cables, is, in its own way, just as reprehensible as Julian Assange's indifference to the fate of vulnerable individual human beings named in the cables.
He of all people should know that the US Government neither has the time, the money , nor the inclination, nor the bureaucratic efficiency to warn or protect the hundreds of named informants or contacts, which have now been betrayed to the world, an action which has been universally condemned by WikiLeakS.org's former mainstream media partners and by human rights organisations.
This is in addition to the names of political dissidents who were in contact with the US Embassy in Belarus which Assange has already handed over to the Lukashenko dictatorship via the holocaust denier Israel Shamir.
Some "open source" / "full disclosure" advocates are making the spurious claim that the publication by WikiLeakS.org of the unredacted cables.csv and onto their searchable web site front end, is somehow better for any political dissidents or confidential sources who had dealings with the US Embassies and whose names are tagged with (strictly protect) and other markers.
Firstly, not all political dissidents in repressive countries have access to the internet at all, let alone to fast, secure, anonymous connections which would allow them to download the massive cables.csv file itself or to use the (insecure) WikileakS.org cable search websites.
None of these websites employ SSL Digital certificates or provide Tor Hidden services etc. to mask the identities of people searching for their own names or those of their family or friends.
Some of the people mentioned in the US Embassy cables several years ago, could in fact be in prison or under investigation for other reasons in 2011, without any or without any safe internet access at all. Being named as having been in contact with the US Embassy, even several years ago, could easily lead to charges of espionage etc. in insane countries like Iran.
Julian Assange's disregard for the Sensitive Personal Data of innocent individuals and his organisation's utter incompetence at handling such data securely, is indistinguishable from that displayed by many of the government bureaucracies you would expect him to be opposed to. Do not to trust him or WikiLeakS.org with any future whistleblower leak material, Find another post WikiLeakS.org website or organisation instead - see the listing and analyses at LeakDirectory.org wiki.
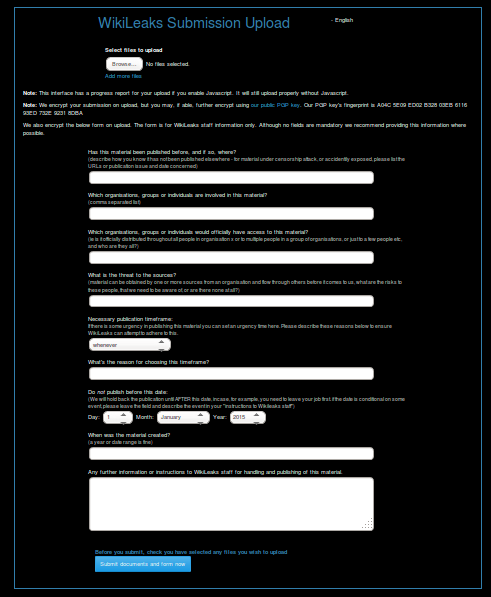
WikiLeakS.org and PGP Public Key Encryption
WikileakS.org abandoned even their limited use of PGP Encryption with the public or with the media, back in 2007, when they let their published PGP key expire.
Why have WikiLeakS.org abandoned the use of PGP Encryption ?
If they had been using Public Key Cryptography last year, to encrypt correspondence or documents or files using their recipients' individual Public Keys, then there would have been no password for the incompetent WikiLeakS.org activists to re-use .
Every copy of the controversial cables.csv file could have been encrypted with a different recipient's Public Key and would have had a different symmetric encryption key (which no human would could have been capable of revealing, even under torture).
Not even WikiLeakS.org / Julian Assange could have decrypted a seized or intercepted or publicly leaked copy of such an encrypted file, only the recipient with access to his or her own private decryption key could have done so.
Either Julian Assange is ignorant of how to use Public Key Cryptography (hardly likely for someone who has tried to write cryptographic software himself) or he and the #wikileaks twitter feed are lying again:
https://twitter.com/#!/wikileaks/status/109134616153169920
Encryption passwords (PGP) are permanent. David Leigh constantly lies, hence even in his own book, "snaky brits".
6.24 AM September 1st 2011
https://twitter.com/#!/wikileaks/status/109136557914603520
@ABCTech It is false that the passphrase was temporary or was ever described as such. That is not how PGP files work. Ask any expert.
6.32 AM September 1st 2011
To decrypt a file encrypted with PGP using a recipient's Public Key, you need to have physical access to the Private De-Cryption key, which is not accessible to anyone who copies or intercepts the encrypted file in transit.
Obviously the password which unlocks the Private De-Cryption Key from your PGP Keyring can be changed.
Symmetric encryption unprotected by Public Key encryption is just an option with PGP, but that is not how PGP is designed to be used to protect files in transit over the internet or on vulnerable USB memory sticks !
There was nothing, except for laziness or incompetence, which prevented Julian Assange or his followers from securely destroying the symmetrically encrypted cables.csv compressed file archive immediately after he gave it to David Leigh and then re-encrypting it from the master copy with a different key and passphrase. This master copy , we assume, given the dispute between Julian Assange and Daniel Domscheit-Berg, would have been held on a separately encrypted computer file system anyway.
The award winning investigative journalist at The Guardian newspaper David Leigh's book:
WikiLeaks: Inside Julian Assange's War on Secrecy by David Leigh and Luke Harding
did reveal on pages 138 to 139 an unnecessary password, which he rightly assumed would only be a temporary one, but which should never have been re-used by Julian Assange in the first place.
Leigh refused. All or nothing, he said. "What happens if you end up in an orange jump-suit enroute to Guantánamo before you can release the full files?" In return he would give Assange a promise to keep the cables secure, and not to publish them until the time came. Assange had always been vague about timing: he generally
indicated, however, that October would be a suitable date. He believed the US army's charges against the imprisoned soldier Bradley Manning would have crystallised by then, and publication could not make his fate any worse. He also said, echoing Leigh's gallows humour: "I'm going to need to be safe in Cuba first!"
Eventually, Assange capitulated. Late at night, after a two-hour debate, he started the process on one of his little netbooks that would enable Leigh to download the entire tranche of cables. The Guardian journalist had to set up the PGP encryption system on his laptop at home across the other side of London. Then he could feed in a password. Assange wrote down on a scrap of paper:ACollectionOfHistorySince_1966_ToThe_PresentDay#. That's the password," he said. "But you have to add one extra word when you type it in. You have to put the word '"Diplomatic' before the word 'History'. Can you remember that?"
"I can remember that."
Leigh set off home, and successfully installed the PGP software. He typed in the lengthy password, and was gratified to be able to download a huge file from Assange's temporary website.
So having given Leigh instructions about downloading and installing PGP software, Julian Assange failed to instruct him to generate a Public / Private key pair and to send him the Public Key, so that Julian could individually encrypt the the cables.csv compressed archive just for David Leigh and nobody else.
At the face to face meeting described in the book, Julian Assange could easily have given David Leigh a copy of a WikiLeakS.org Public Encryryption Key for him to install when he set up the PGP software on his laptop as instructed, or pointed him to an online version.
They could have agreed a pre-shared secret for extra authentication.
David Leigh could then have been instructed to generate his own Public / Private keypair (protected in his PGP Keyring by his own strong passphrase) and to send a Digitally Signed and Encrypted copy of his Public Key back to Jullian Assange via email etc. together with the pre-shared authentication secret, all encrypted with the WikiLeakS.org Public Key. This should have been sufficient cryptographic proof that David Leigh's Public Key was the correct one, since nobody else apart from Julain Assange / WikiLeakS.org could have read the contents of that message.
Julian Assange could then have encrypted the compressed cables.csv file with David Leigh's Public Key and pointed him to the secure website he had set up for the encrypted file to be downloaded from
This encrypted file could only have been de-crypted by someone in possession of both David Leigh's passphrase and the corresponding Private Key in the PGP Keyring on David Leigh's MacBook laptop.
If WikiLeakS.org had been regularly using PGP over the years, even inexperienced members of the cult would have been familiar with these simple, well documented concepts.
If that copy of the encrypted file had somehow been published by the incompetent WikiLeakS.org crew on BitTorrent, then only David Leigh could have decrypted it (assuming he was still in control of his PGP Keyring on his laptop computer) , even if he had published his own pass phrase in his book, rather than Julian's rather pompous one.
7-Zip compression
Then he realised it was zipped up - compressed using a format called 7z which he had never heard of, and couldn't understand.
The .7z file extension is used by 7-Zip . This is freely available over the internet, on various computing platforms and does offer more options for better compression than the standard .zip compression utilities which are built in to modern versions of the Microsoft Windows or Apple OSX operating systems, at the cost of longer compression times and more use of memory.
The 7-Zip Ultra compression option seems to be what the cables.csv file was compressed with down to i.e. only 21 % of its original size.
However to achieve this amount of compression on such a big file could take quite a while, perhaps up to an hour on an average PC. Unzipping is much quicker, a couple of minutes at most.
Compression is also built in to the PGP / GnuPG encryption software, but that produces a compressed file of about 640 MB i.e. about twice that of the of the 7-Zip version, about 41% of the original size of the monolithic cables.csv file.
Like most .zip compression software these days, 7-Zip also offers encryption, using the same AES 256 bit algorithm used by default by GnuPG / PGP, but Assange et al did not bother to make use of that.
He got back in his car and drove through the deserted London streets in the small hours, to Assange's headquarters in Southwick Mews
Assange was staying at Vaughan Smith's Frontline Club for investigative / foreign / war correspondent journalists, owned by Vaughan Smith, in whose Norfolk country estate has bedrooms at numbers 7 and 9 Southwick Mews
http://www.frontlineclub.com/club/bedrooms-1.php
He is now on bail and electronically tagged living at Vaughan Smith's country estate in Norfolk, where his supporters invent state surveillance fantasies for the credulous mainstream media - see "CCTV ANPR" or just "radar activated speed signs" monitoring Julian Assange at Ellingham Hall in Norfolk ?
Assange smiled a little pityingly, and unzipped it for him.
Now, isolated up in the Highlands, with hares and buzzards for company, Leigh felt safe enough to work steadily through the dangerous contents of the memory stick.
So, in the end, Julian Assange in fact actually handed over an unencrypted copy of the file to David Leigh, on an easily lost or stolen USB memory stick. If Assange really cared about protecting innocent people from evil governments, then he would not have allowed this to happen.
It is astonishing how the WikiLeakS.org cult propaganda machine has deluded itself that somehow it was David Leigh and The Guardian which was responsible for this cryptographic and internet publication incompetence, rather than the alleged technological privacy and anonymity expert Julian Assange and his supposedly expert helpers.
TextWrangler keyword search
Obviously there was no way that he, or any other human, could read through a quarter of a million cables. Cut off from the Guardian's own network, he was unable to call up such a monolithic file on his laptop and search through it in the normal simple-minded journalistic way, as a word processor document or something similar: it was just too big. Harold Frayman, the Guardian's technical expert, was there to rescue him. before Leigh left town, he sawed the material into 87 chunks, each just about
small enough to call up and read separately.
Probably 19 Megabytes for each of 86 chunks with a little bit left over in the 87th chunk.
Then he explained how Leigh could use a simple program called TextWrangler
TextWrangler is the "little brother" of BBEdit and is only available for the Apple Macintosh platform. David Leigh's laptop computer.is stated to have been a MacBook elsewhere in the book.
to search for key words or phrases through all the separate files simultaneously, and present the results in a user-friendly form.
So why had Julian Assange or his WikiLeaks acolytes not already broken the 1.6 Gigabyte file down into usable chunks and zipped them up into, ideally, several archive files for their mainstream media partners ?
This WikiLeak.org blog has criticised them in the past for not offering (multiple) floppy disk or even CD-ROM sized versions of their whistleblower leaks documents, as well as just large monolithic files.
Not everybody, especially people in third world countries under repressive governments, or even people using mobile internet devices, has access to fast broadband internet connections.
Is this the end of WikiLeakS.org ?
Now that WikiLeakS.org have no more secrets left to publish, will they actually get around to re-inventing themselves and re-launching a secure anonymous system without the destructive influence of Julian Assange ?
Or will the cult continue regardless and just get dragged into long legal cases ?


















Recent Comments