Spy Blog and others, try to be vigilant about UK Government, schemes involving technological systems and infrastructures which, if not operated honestly, transparently and under strict control, could easily be abused to betray our freedoms and liberties, either now or in the future.
The Conservative / Liberal Democrat coalition government appear to be, for no good reason, persisting with the stupid web censorship plans championed by the authoritarian, former hardline Communist, former Labour Home Secretary John "not fit for purpose" Reid (who is now a paid consultant to multi-national private security companies bidding of public sector contracts e.g. EU Plans for Internet Censorship
According to this misspelled Home Office press release web page, there is now a secretive, unaccountable Web Censorship quango, with a web form for allegedly "anonymous" denunciations:
Challenge online terrorism and extremism
Thursday, 07 Apr 2011
Information leaflets and posters have been sent to every police force in the UK advising the public on how to identify and report offensive or illegal content.
"Information leaflets and posters", to promote a world wide web based campaign - surely this is not the correct media communications strategy ?
- How many leaflets and posters have been distributed ?
- Have the spelling mistakes in this Press release web page also found their way into the printed material ?
- How much public money has this cost ?
It promotes an online tool - which can be found on the Directgov website (new window) - that allows people to report material anonymously.
Challenge and report
Security minister, Baroness Neville-Jones, said that it's vital that online extremisim is taken seriously: 'I want to encourage those who come across extremist websites as part of their work to challenge it and report it through the DirectGov webpage.
'By forging relationships with the internet industry and working with the public in this way, we can ensure that terrorist use of the internet does not go unchallenged.'
"extremisim" [sic] should presumably be spelled "extremism"
Why not use the existing MI5 Security Service or the Metropolitan Police secure online web forms then ?
Websites reported to Directgov via its online form are referred to the national Counter Terrorism Internet Referral Unit.
The specialist team of police experts work with industry and partners in the UK and abroad to investigate and take down illegal or offensive material if neccessary.
"neccessary." [sic] Does the Home Office Press Office really have no access to spell checkers ? Surely all Civil Servants should be able to spell "necessary", something which some of them, clearly, are not ? Presumably "national" should also start with a capital letter.
- Who is the person in charge ?
- Who exactly are these "partners in the UK and abroad" ?
- How can they be contacted by the public, apart from via this allegedly "anonymous" web form ?
- How is their effectiveness and value for money assessed and by whom ?
- What are the mechanisms for detecting and correcting the mistakes and "collateral damage" that they will inevitably make ?
- How is this website reporting and takedown mechanism compatible with the stated European Union policies on the topic, which stress that they must not damage the fundamental human rights of freedom of speech and association etc. ?
Past successes
In the last year, reporting through Directgov has helped the government remove content which has included beheading videos, terrorist training manuals and calls for racial or religious violence.
Successes include:
* removing a number of videos encouraging martyrdom operations that had been uploaded to a UK-based website
* shutting down a website that provided detailed video instructions on bomb making
* removing a number of videos encouraging acts of terrorism from a social networking siteTo report content visit the Directgov website (new window) .
Have any of these "successes" actually involved websites physically hosted in the United Kingdom ?
Have any of them involved invoking the "takedown notice" legal powers under the controversial Terrorism Act 2006 sections 1 to 4, Encouragement etc. of terrorism ?
Is this web form really "anonymous" ?
Has the Marsham Street kremlin learned anything about running an anonymous whistleblower website submission form, from the likes of WikiLeaks.org and its couple of other emulators ?
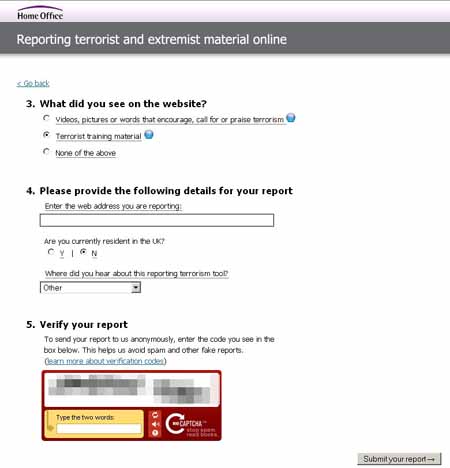
The actual web form is at
https://reporting.direct.gov.uk/
It claims:
This website is intended for the public to report any illegal terrorist or violent extremist information, pictures or videos found online. The report only takes a few minutes to complete, and all reports received are anonymous and reviewed by specialist police officers.
Weaknesses which could have been avoided:
Is the web form "secure" ? Probably, but it is not configured as professionally as it should be.
SSL Digital Certificate
Incredibly, for a system which involves national security intelligence gathering reports, the SSL / TLS encryption is misconfigured on the reporting.direct.gov webserver.
It only rates a C: [52] rating from SSLLabs
It is unprofessional to configure any public web server with a Digital Certificate, without disabling the weak 40 bit and 56 bit cipher options, which can easily be broken in real time by today's personal computers.
There is no excuse for not disabling the deprecated SSL 2.0 protocol either.
Details
Certificate Information
Common name reporting.direct.gov.uk
Alternative names -
Prefix handling Not required for subdomains
Valid from Wed Jan 27 00:00:00 UTC 2010
Valid until Fri Jan 27 23:59:59 UTC 2012 (expires in 9 months and 25 days)
Key RSA / 1024 bits
Signature algorithm SHA1withRSA
Server Gated Cryptography Netscape Step-Up
Weak key (Debian) No
Issuer www.verisign.com/CPS Incorp.by Ref. LIABILITY LTD.(c)97 VeriSign (OU)
Next Issuer Class 3 Public Primary Certification Authority (OU) TRUSTED
Chain length (size) 2 (2221 bytes)
Chain issues None
Validation type Not sure
Revocation Information CRL, OCSP
Revocation Status Good (not revoked)
Trusted Yes
Protocols
TLS 1.2 No
TLS 1.1 No
TLS 1.0 Yes
SSL 3.0 Yes
SSL 2.0+ Upgrade Support Yes
SSL 2.0 INSECURE Yes
Cipher Suites (sorted by strength; server has no preference)
TLS_RC4_128_EXPORT40_WITH_MD5 (0x20080) WEAK 40
TLS_RC2_128_CBC_EXPORT40_WITH_MD5 (0x40080) WEAK 40
TLS_RSA_EXPORT_WITH_RC4_40_MD5 (0x3) WEAK 40
TLS_RSA_EXPORT_WITH_RC2_CBC_40_MD5 (0x6) WEAK 40
TLS_RSA_EXPORT_WITH_DES40_CBC_SHA (0x8) WEAK 40
TLS_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA (0x14) DH 512 bits (p: 64, g: 1, Ys: 64) WEAK 40
TLS_DES_64_CBC_WITH_MD5 (0x60040) WEAK 56
TLS_RSA_WITH_DES_CBC_SHA (0x9) WEAK 56
TLS_DHE_RSA_WITH_DES_CBC_SHA (0x15) DH 1024 bits (p: 128, g: 1, Ys: 128) WEAK 56
TLS_RC4_128_WITH_MD5 (0x10080) 128
TLS_RC2_128_CBC_WITH_MD5 (0x30080) 128
TLS_RSA_WITH_RC4_128_MD5 (0x4) 128
TLS_RSA_WITH_RC4_128_SHA (0x5) 128
TLS_RSA_WITH_AES_128_CBC_SHA (0x2f) 128
TLS_DHE_RSA_WITH_AES_128_CBC_SHA (0x33) DH 1024 bits (p: 128, g: 1, Ys: 128) 128
TLS_DES_192_EDE3_CBC_WITH_MD5 (0x700c0) 168
TLS_RSA_WITH_3DES_EDE_CBC_SHA (0xa) 168
TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA (0x16) DH 1024 bits (p: 128, g: 1, Ys: 128) 168
TLS_RSA_WITH_AES_256_CBC_SHA (0x35) 256
TLS_DHE_RSA_WITH_AES_256_CBC_SHA (0x39) DH 1024 bits (p: 128, g: 1, Ys: 128) 256
Miscellaneous[...]
Server signature Apache/2.2.3 (Red Hat)
Server hostname reporting.direct.gov.uk
Session resumption Yes
Renegotiation Secure Renegotiation Supported
Strict Transport Security No
TLS Version Tolerance 0x0304: 0x301; 0x0399: 0x301; 0x0499: fail
PCI compliant No
FIPS-ready No
Ephemeral DH 512 bits (p: 64, g: 1, Ys: 64) WEAK
The other two web forms which solicit national security or crime related information e.g.
MI5 the Security Service, get a much better rating of: A [85]
as does the Metropolitan Police's online crime reporting web form, which also gets a rating of A: [85]
Most modern web browsers will usually connect with this web server using strong encryption (at least 128bit encryption). However the deprecated SSL 2.0 protocol could be used in combination with a man-in-the-middle attack (e.g. invoking a rogue wireless access point) to force the use of weak 40bit or 56bit encryption, which can be easily broken in real time , on today's computer hardware.
Why is there only space for a URL ?
What exactly do they hope to gather which Google has not already indexed ?
Even if you believe that it is a good idea to simply collect suspicious web URLs, it should be obvious from previous convictions, let alone ongoing investigations, that most criminal content available via the world wide web will be on password protected private web forums etc..
There is nowhere on this Report form to supply a username and password to such private areas, something which prevents Google or other search engines from already having accessed and indexed these.
There is no way of adding any comments or context or background information.
Using Google Re-Captcha for this form is wrong !
It is reasonable to use a Captcha system, running from the UK based Direct.gov.uk servers, to reduce the amount of script driven spam which this web form will attract.
Instead, the web form uses the Google operated Re-Captcha running from servers in the USA.
This is totally wrong for a United Kingdom based terrorism intelligence gathering system from the perspective of public trust and the promises made about "anonymity" !
Why should Google, a foreign based company (and therefore the US government) be handed over the internet address and web browser details of every supposedly "anonymous" terrorism information related report ?
Every time the Reporting form is loaded, the Google Re-Captcha web and application servers will log your IP Address and web browser details as the graphical images are pulled across from the USA.
Google will also have log file details every time the Re-Captcha codes are filled in and submitted i.e. they will be easily able to tell which visitors to the web form have actually submitted something.
If you are planning to use this web form "anonymously" as promised, then you need to:take precautions before accessing https://reporting.direct.gov.uk
- Make sure that you are not logged in to any Google products e.g. gmail or , on your Android smart phone, Google Latitude etc.
- Delete any Google cookies
- Use Tor or other methods of hiding your traceable IP address.
otherwise you will risk your "anonymity", which could have serious consequences for you, either from the terrorists or extremists you are reporting on, or from the bureaucratic police and intelligence agencies you are reporting to.
N.B. There is history of this sort of failure to to protect the anonymity of potential informants via the internet within the Whitehall securocrat establishment. See the Spy Blog category archive: MI5 email subscriptions
How is this intelligence data being transmitted from the web server to the CTIRU ?
- Can we be sure that the "report form" data is not being kept unencrypted on the reporting.direct.gov.uk webserver ?
- Is it being emailed in a plaintext, unencrypted format ?
- Is it available for download through unencrypted protocols like FTP ?
There is no public promise that proper encryption techniques are being used, so we must assume that they are not.
Are there any good points about this form at all ?
Feedback Reference Code
A major failing of the MI5 Security Service SSL encrypted national security / terrorism "reporting suspected threats" form, is that there is never any acknowledgement that the information you supply has actually been received, let alone read, let alone acted upon.The form is a one way, information "black hole", which discourages everyone from ever using it more than once.
This reporting.direct.gov.uk web form does at least have a supposedly random reference ID code which can be used to bookmark the web page for you to come back later, and perhaps get some idea of any further action that the Counter Terrorism Internet Referral Unit may have got around to.

This promises:
Thanks for your referral. It is currently
being assessed Please check back at this page
for further updates in four to six days.
It is too early to tell if they will actually give people who have reported a URL, any meaningful feedback, but there is always hope.
Conclusion
This supposedly secure and "anonymous" terrorist related reporting system has been allowed to go live to the public, without these basic security and anonymity flaws being noticed and corrected.
Home Office politicians and senior officials, Police and Intelligence Agency officials etc. appear to have learned nothing from their past failures under the Labour government.
Why were the GCHQ / CESG ("The National Technical Authority for Information Assurance") people not involved in checking this web form and web server, before it was allowed to go public ?
N.B. we do not totally blame the American internet consultant, who appears to have
Designed, built and launched site for SO15's Counter Terrorist Internet Referral Unit, which allows reporting of websites in breach of the Terrorism Acts; defended the site against a wave of hacker attacks after the site was Slashdotted
[We have omitted details of his name, email addresses, mobile telephone number, personal web site and probable home address in London]
The Senior Responsible Owner of this government project, should take public responsibility for its failings.
Is there actually one person in charge, or is decision making evaded somewhere between ACPO, the Metropolitan Police and the Home Office ?
This also reflects badly on the level of internet expertise within the Counter Terrorism Internet Referral Unit.
If they cannot instantly recognise weaknesses in their own web form, what use will they be against anything but the simplest of terrorist or extremist websites ?
Our fear is, that through ignorance, they will then cause "collateral damage" to innocent websites or IP addresses, through over-broad Terrorism Act 2006 section 3 "takedown orders" , or through the physical seizure of computer hardware which hosts innocent people's websites or through the legal intimidation of domain name registrars.
The Home Office press office should get a spell checker for their web page press releases.
UPDATE: 1st May 2011:
Spy Blog is glad to note that the Digital Certificate problems with
seems to have been fixed i.e no more deprecated SSL 2.0 protocol and no more weak cipher suites.
This now gets an A [85] rating from the SSLabs test page:
https://www.ssllabs.com/ssldb/analyze.html?d=reporting.direct.gov.uk
There are still problems with the use of Google's Recaptcha in the USA at all and also the Digital Certificate for the link to the Recaptcha code
https://api-secure.recaptcha.net
This Digital Certificate expired nearly a year also and also seems to suffer from SSL 2.0 and weak cipher suites etc.
https://www.ssllabs.com/ssldb/analyze.html?d=api-secure.recaptcha.net
Perhaps this should be using
https://www.google.com/recaptcha/api/challenge?k=6LfH6wkAAAAAACLBp7RyVVFu7xZRiRxqBTct_gtN
rather than
https://api-secure.recaptcha.net/challenge?k=6LfH6wkAAAAAACLBp7RyVVFu7xZRiRxqBTct_gtN
The best feature of the web form, the feedback tracking could be improved slightly. Unless someone has actually bookmarked the Tracking Report Status page, there is no link to
https://reporting.direct.gov.uk/status.php
in the workflow of the the web form for them to type their Response Code into, assuming that they have written it down or remembered it.
Saving the web page or bookmarking it does poses potential anonymity betrayal risks to anybody who is trying to report their concerns about a web page or website from within an organisation or company etc. - it could tip off their colleagues who might be up to something illegal.
The Home Office also does now appear to have corrected the spelling mistakes on their web page press release.





























Recent Comments