Overall, the short BBC2 tv documentary series Who's Watching You ? was of considerable interest, but our initial criticism still stands - they tried to cover far too many "surveillance" topics, several of which need much more explanation and analysis, for the public and politicians to be properly informed about their implications.
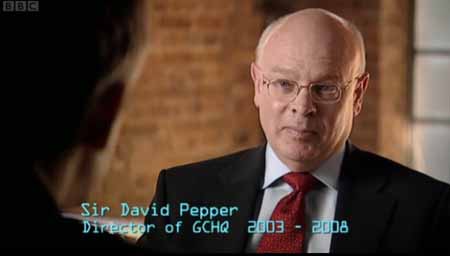
Despite getting face to face interviews with important Surveillance Database State policy makers (or recently retired ones, at least), like the then Home Secretary Jacqui Smith (who was re-shuffled during the screening of the series) and Sir David Pepper KCMG, who retired as head of GCHQ in 2008 (replaced by Iain Lobban CB), they either did not ask enough questions, or, more likely, most of the interesting stuff was censored out before transmission.
We have transcribed a few lines from this TV programme below, from the good quality interviews broadcast or streamed in clear English.
This process of transcription (try it for yourself), illustrates just how time consuming and expensive and error prone this must be, for poor quality recordings, with background noises, perhaps in foreign languages or obscure dialects, perhaps using innocent sounding code phrases, done in a hurry by GCHQ or other intelligence agency or police transcribers, translators and intelligence analysts.
When Sir David Pepper was explaining, in very simplistic terms, the difference between Plain Old Telephone System switched line interception and Voice over IP internet router interception, he was allowed to pooh pooh the absolutist 100% interception and snooping scenario straw man.
Richard Bilton (RB) interviewed Sir David Pepper (DP)
RB: That is a classic myth, isn't it, or it's what people believe, they imagine that, they make a phone call, and they say "bomb", and that you will immediately know about it.
DP:Alright, well, there's, there's two reasons why that is, is, just wrong. One is it, it, implies technology which is just, errm, in your dreams, I think.
But the other reason is, one of Authority. What GCHQ and the other Agencies are not allowed to do, is to listen to everybody's phone calls., all the time, just in case they happens to be something there, that, that, that's, useful.
There are very stringent processes in place to control, who can be listened to, who can be monitored, and when, and for how long.
Except that, unlike many other countries, there is no involvement of any independent Judges or Magistrates in the granting of permission for such extraordinary and exceptional invasions of privacy and human rights, as with normal Search Warrants, based on Reasonable Suspicion or Just Cause. There are no publicly transparent and democratically accountable "stringent processes", only the fig leaf of the almost powerless Regulation of Investigatory Powers Commissioners.
Similarly, in the piece broadcast on BBC News 24, which is obviously part of the same interview:
RB: If you take that to its extreme, then, could you have a completely secure State, if you had 100 per cent surveillance ?
DP: ermm, you'd have to have, so many people involved in the security services, that I'm not sure what anyone else in the country would be doing.
This a very easy straw man argument, allowing Sir David to sound reasonable, whilst ignoring the real issues of proportionality and public trust.
You do not need "100% surveillance" to create a repressive police surveillance database state, in the same way that a commercial company only really needs to control say 40 per cent of a market, in order to be, effectively, a monopoly.
There was of course no way of knowing whether you were being watched at any given moment. How often, or on what system, the Thought Police plugged in on any individual wire was guesswork. It was even conceivable that they watched everybody all the time. But at any rate they could plug in your wire whenever they wanted to. You had to live -- did live, from habit that became instinct -- in the assumption that every sound you made was overheard, and, except in darkness, every movement scrutinised.
George Orwell - 1984, part 1, chapter 1
Neither Sir David Pepper, nor the disgraced former Home Secretaries Jacqui Smith, nor the doubly disgraced David Blunkett (who also weaseled his way on screen, but refused to quantify how many Regulation of Investigatory Powers Interception Warrants he had ever refused to sign) bothered to explain exactly why it is at all proportionate for their insecure mass surveillance systems, to be aimed at millions of innocent people, rather than being narrowly targeted only at real criminals.
The programme allowed Sir David Pepper and David Blunkett to claim that Interception Warrants are not somehow "rubber stamped" by the relevant Secretary of State (in the case of GCHQ, that is the Foreign Secretary), but the given the vast numbers of these (thousands a year) and the low calibre of the Labour politicians who have been Cabinet Ministers, this is nonsense.
Even an honest, hard working and intelligent Home Secretary or Foreign Secretary, (when will we get one of those ?) , should really be concentrating on other policy matters, not on the detail of thousands of surveillance snooping cases. An amendment to RIPA via the Terrorism Act 2006, does , in fact, allow secret "officials" to rubber stamp such RIPA warrants, instead of the Home or Foreign Secretary personally signing each one.
This third programme did not properly discuss the Government's vast Communications Traffic Data Retention powers, and centralised database plans, even though the programme showed a couple of examples of criminal cases which had been investigated and prosecuted with the help of Communications Traffic Data, even though Sir David Pepper and Jacqui Smith could and should have been questioned about this,which is far more prevalent, and even less controlled than the Interception of electronic communications.
This week's episode also included several "neighbourhood watch" type schemes which seem to have been corrupted into "community watch" schemes, funded by the Home Office, feeding information into the Security Service MI5 / Regional Police Counter-Terrorism Unit "Rich Picture" intelligence databases.
The people involved, rightly recognise that it is part of their local communities responsibility not to leave "anti-terrorism resilience" just to the Police or Intelligence Agencies.
However, there really is no transparent, democratic accountability of any sort , to provide proper scrutiny and oversight of such schemes, whether in Muslim communities in Derby or on the West Coast of Scotland, which is somehow thought to "vulnerable" to the landing by sea, of a Mumbai style terrorist murder squad.
Richard Bilton (RB) interviewed John Laurie (JL), from the Dumfries & Galloway Constabulary's Port's Unit:
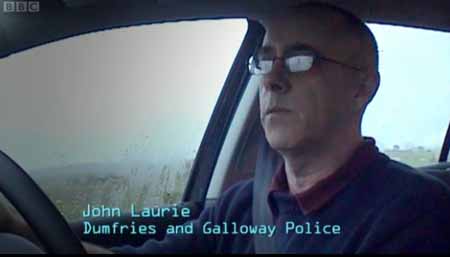
JL: I think that, err, the 4x4 ending up in the middle of Glasgow airport, proves that things are going to happen up here.
The more contacts we have, the more information we can gather, about normal routines, in an area, that means we can pick out the, awkward, or the, strange event, and hopefully prevent someone using or our area, to carry out an attack on the UK.
Since John Laurie and his volunteer coastwatchers are unarmed, what exactly are they going to do if they ever did accidentally stumble over a squad of terrorists armed with AK-47 assault rifles ?
RB: But they are..it's like a Network of, of Spies, isn't it ? In a , in a basic sense, they are the eyes and ears of the Security Services ?
JL: I suppose, in some ways that's true, ..., err, err, to be honest, I wouldn't know a Spy , if I was to trip over the top of one.
How exactly is a Terrorist any different in appearance or behaviour, from a Spy ?
How are John Laurie, or his coastwatchers / spies, expected to know what a terrorist looks like ?
What about the "normal" activities looking of both criminal smugglers and of innocent tourists ?
Will the age old "you ain't from around here, are you boy ?" attitude of suspicion towards, and unwarranted discrimination, or worse, against strangers prevail ?
N.B. many of the film locations in the classic 1973 cult horror film The WIcker Man , were actually filmed in Dumfries and Galloway.



























I found Sir David Pepper's analysis of the difficulty of intercepting packet-switched network traffic incomplete. The section used in the
programme claimed that it is now very difficult to intercept such traffic.
Crucially, however, in the graph of routers he drew, he did not show the entry point to the network used by the surveillance target - ie:
his ISP or 3G/GPRS telecoms provider.
Unless the target is using multiple network interfaces (and different ISPs or telcos) simultaneously, instructing the target's single ISP to set up a wiretap on that connection is simplicity itself.
@ Michael - even Sir David's simple drawing of a line between two points, belies a lot of technological complexity in intercepting even Plain Old Telephone System landline voice telephone calls.
His simplistic little network of routers, and the few words of his which explained a bit about them and Voice over IP does give the impression that he neglected to mention the ISP endpoints.
However, it is true that Peer to Peer Voice over IP systems, like Skype,
http://en.wikipedia.org/wiki/Skype
which use strong encryption tunnels between local nodes, and super nodes, which may be hosted on machines in different ISPs, and even in different countries, means that not all of an intercepted Skype Voice over IP conversation can be easily stitched together, without the collusion of Skype (which may or may not be available to GCHQ).
Similarly with Mobile Phones, all the second generation GSM phone calls are only (weakly) encrypted over the air between the handset and the cell transmitter base station, once they pass onto the the wired infrastructure, they are in the clear, via GPRS Tunneling Protocol and can be snooped on centrally.
With 3G phones, the voice traffic (but not, in practice, the data traffic) is also encrypted over the wired infrastructure, and the Home Location Register, which holds the cryptographic keys, may be located in a foreign country.
Hence the requirement for spending billions of pounds to upgrade GCHQ's computing and interception capacity, in the hope that they can stitch together most of a VoIP call , most of the time, and, perhaps de-crypt it on the fly as well.
Neither of these major problems for lawful, or even for illegal, phone call Interception make much difference for Communications Traffic Data collection or analysis, which is much easier to collect, and which is usually at least as useful to an investigation as actual intercepts of voices, which may be speaking in a pre-arranged code or obscure foreign dialect anyway.