It is hard to see how Yet Another Censored Report by the Intelligence and Security Committee into the 7th July 2005 London bomb attacks will satisfy the victims and their families and many others, who want an actually independent Public Inquiry.
They still have not bothered to examine any possible links with the failed 21st July 2005 attacks.
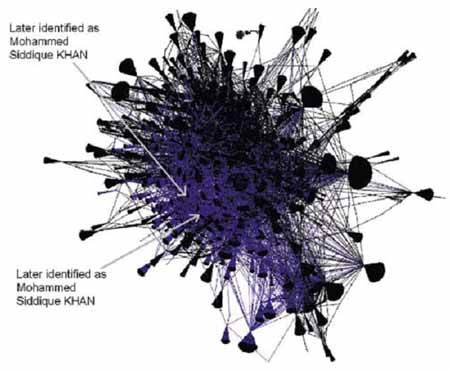
There are a couple of points of more general interest, such as a graphical illustration of searching for a needle in a haystack involved in Communications Data Traffic Analysis, and some explanation of some technical jargon, which might interest tv and film scriptwriters or fiction novelists.
The scale of Operation CREVICE is demonstrated by the following diagram. It shows all calls assessed to relate to international counter-terrorism, between unique parties, between 1 January and 1 April 2004 (with each line representing one or more calls). There are *** unique numbers (tens of thousands) with *** links between them. Of these, 4,020 are linked to CREVICE. The vast majority of these were eventually assessed not to be related to the bomb plot itself, or even to the wider facilitation network, and were in fact wholly innocent or irrelevant. Each was a potential lead, however, that had to be checked to see if it was relevant or not. The diagram identifies two numbers which were later associated with Mohammed Siddique KHAN.
Of course, Jacqui Smith's plans for Communication Data Traffic Retention and Data Warehousing would simply throw several more haystacks full of data at such a problem - a waste of resources, with horrible privacy and security implications for millions of innocent people.
Some bits of jargon for future Spooks style tv or film drama script writers or spy fiction authors:
-
Contacts and "housing"
Surveillance teams are often tasked by investigators to establish patterns of activity involving the main targets. When a primary target such as KHYAM comes into contact with other individuals, the surveillance team then has to decide whether to follow the new contact or whether to ignore them in favour of staying with the main target. A whole series of factors will be taken into consideration, such as *** ***, etc. This is often a split-second decision by the surveillance team and would later be reviewed as part of the wider investigation.
Following the new contact may mean "housing" them. This means establishing a link between a person and an address with which they appear to be connected so that, if necessary, further inquiries can be pursued at a later date. Essentially it provides a reference point to come back to in the future if the person being followed looks to be of interest.
Over the final six weeks of Operation CREVICE, the police recorded a total of 1,154 vehicles connected to KHYAM in some way (the vast majority of these were innocent or irrelevant connections). MI5 "housed" approximately *** people in these cars (i.e. followed them to one or more addresses). The Metropolitan Police Service "housed" approximately *** subjects. As a matter of routine, checks similar to those described below would have been completed on each occasion.
Levels of checks undertaken by the police
There are four levels of checks that the police carry out when following up leads from investigations. Level 1 and 2 checks are the most basic, and include information on the Police National Computer, police intelligence systems, vehicle registrations and the electoral register. Checks at levels 3 and 4 include progressively more sources of information (for example, level 3 checks may include beneits and council tax records, and level 4 checks may include checks with credit reference agencies and utility companies). The level of checks actually undertaken will depend on the nature of the investigation and the relative importance of the subject or target.
MI5's investigative categories (in 2004/05)
Essential - An individual who is likely to be directly involved in or have knowledge of plans for terrorist activity, or an individual who may have knowledge of terrorist activity.
Desirable - An individual who is associated with individuals who are directly involved in or have knowledge of plans for terrorist activity or who is raising money for terrorism or who is in jail and would be an essential target if at large.
Other> - An individual who may be associated with individuals who are directly involved in, or have knowledge of, plans for terrorist activity.
Remember that "associated" could simply be via the vague sort of "friendship tree" based on phone records illustrated above, which can exponentially sweep up millions of innocent people.
These categories were fluid and, depending on the latest available intelligence, targets might move between them.33
33 MI5 now use "Priority 1" and "Priority 2" as their major investigative categories for networks and plots (with "Priority 3" and "Priority 4" replacing "Other"
- N.B. The only time that MI5 appear to delete or anonymise data which they collect seems to be by accident:
46 The Committee has asked MI5 what happened to these targets, but has been told that the computer records holding the information (from which these figures were obtained) are no longer accessible following an update of their IT systems.
- "cluster" -
74 A "cluster" is a secure form of communication/messaging system used by MI5 and the police that contains operational intelligence and requests for information/checks to be carried out.
- Operation Wedge -
This cluster also shows that there was no Automatic Number Plate Recognition (ANPR) trace for the Honda Civic on 3 March 2004, but that "the details have since been entered on Operation WEDGE". (The ANPR system enables police units to identify vehicles from registration plates, and is used when the vehicle is suspected of involvement in crime or where intelligence is needed on the vehicle. The details of the Honda Civic are not added to the WEDGE counter-terrorism database, contrary to the cluster message.)
How does Operation Wedge relate to the gobbling up of the data (in real time, in bulk) from two London Congestion Charge Zones, London Low Emission Zone all of which use ANPR, into a Metropolitan Police counter-terrorism database ? See Home Secretary Jacqui Smith cripples the Data Protection Act regarding the London Congestion Charge ANPR Mass Surveillance scheme



























As Roderick Jones, the former Special Branch officer and researcher into the potential abuse of massive international online multiplayer games for terrorist or organised criminal purposes comments on the diagram above:
It is not just more haystacks, but entire harvests of utterly different crops which would have to be efficiently and accurately sifted through these days.
Even very fast Deep Packet Inspection hardware plugged into the core internet and telecommunications infrastructure, is going to initially struggle and then eventually fail to catch future plots like this one, since the human translation and intelligence analysis of such a deluge of mostly irrelevant data will never keep up.
It must be relatively easy and very cheap for enemy terrorists or foreign governments or organised criminals, to create false "electronic chatter" about plausible but fake plots, perhaps involving a few gullible and disposable young people who have been "groomed" online by agents provocateurs.
These will divert and distract large numbers of intelligence agency and police resources, which rely too much on electronic snooping.
Baroness Pauline Neville-Jones , the former head of the Joint Intelligence Committee, is scathing about the Intelligence and Security Committee's lack of independence and lack of its own investigative resources.
http://www.guardian.co.uk/commentisfree/2009/may/19/july7-terorism-report
It seems that even the 'Essential' suspects were not picked up prior to the events of 7/7
See
http://preview.tinyurl.com/q6vgct